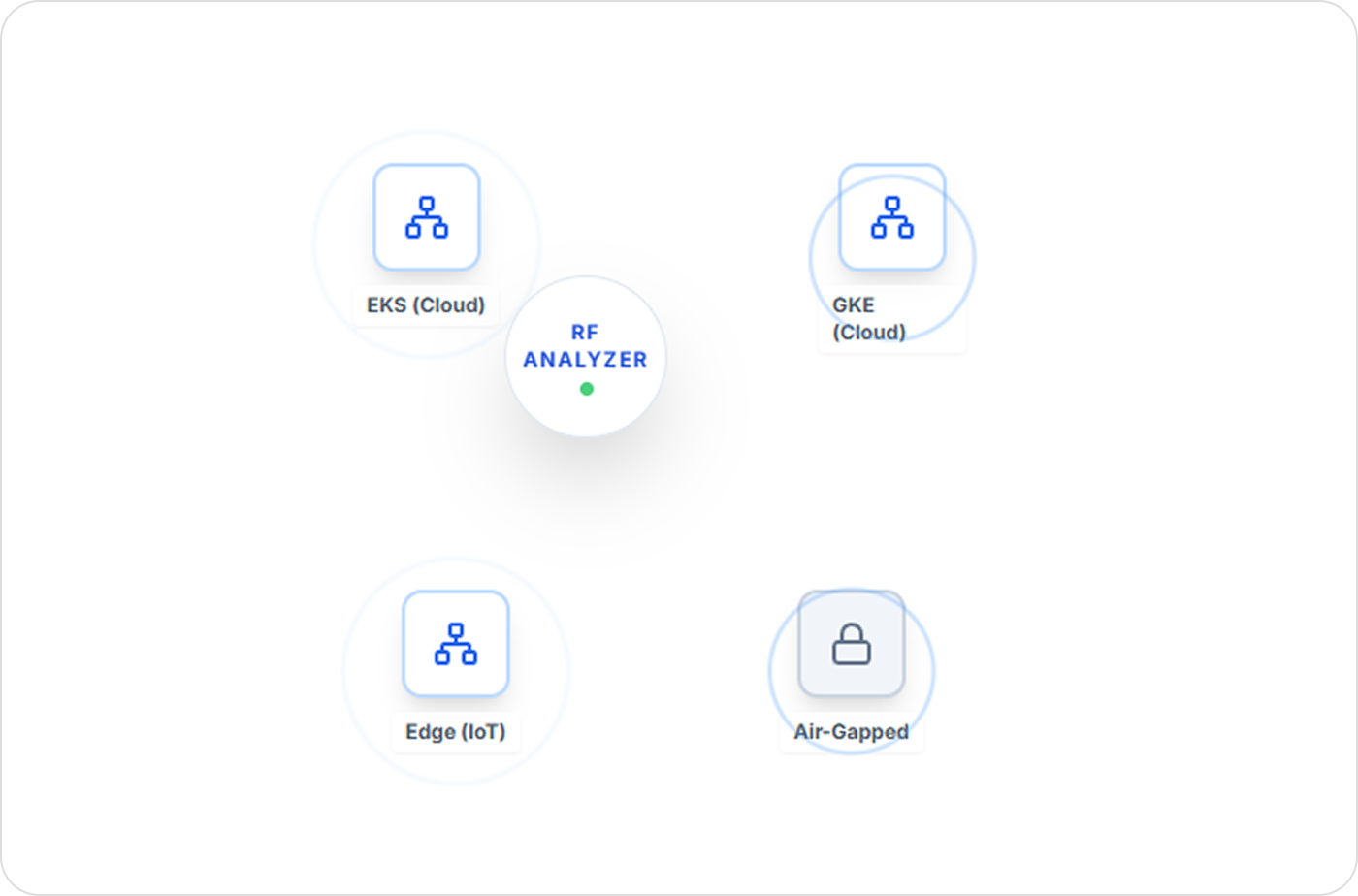
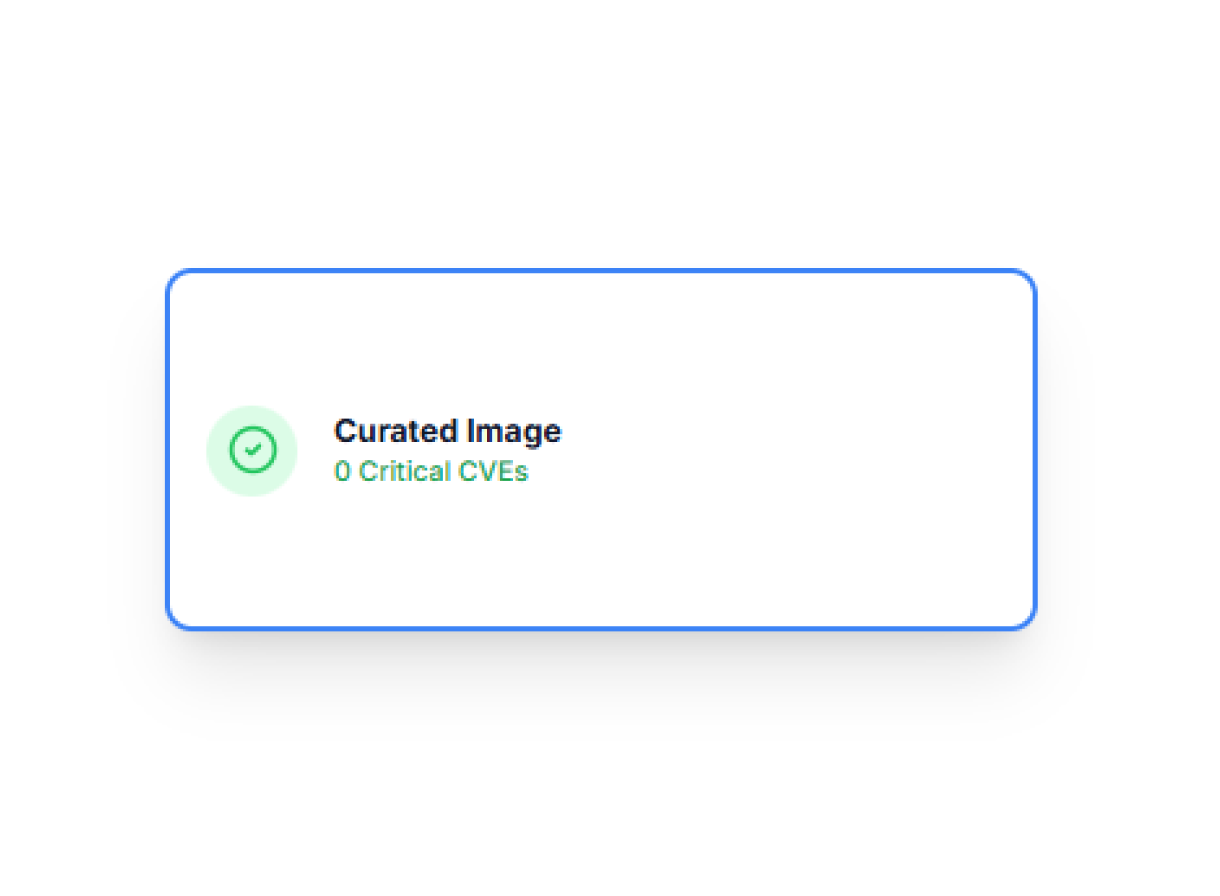
RF Analyser performs full-file, full-package, and configuration-level analysis across Docker, Podman, and Kubernetes workloads. It discovers everything inside an image - not only what package managers report - and validates every CVE using RapidFort’s curated advisory dataset and AI-driven RapidRisk scoring. The result: clean, reliable findings you can act on confidently.