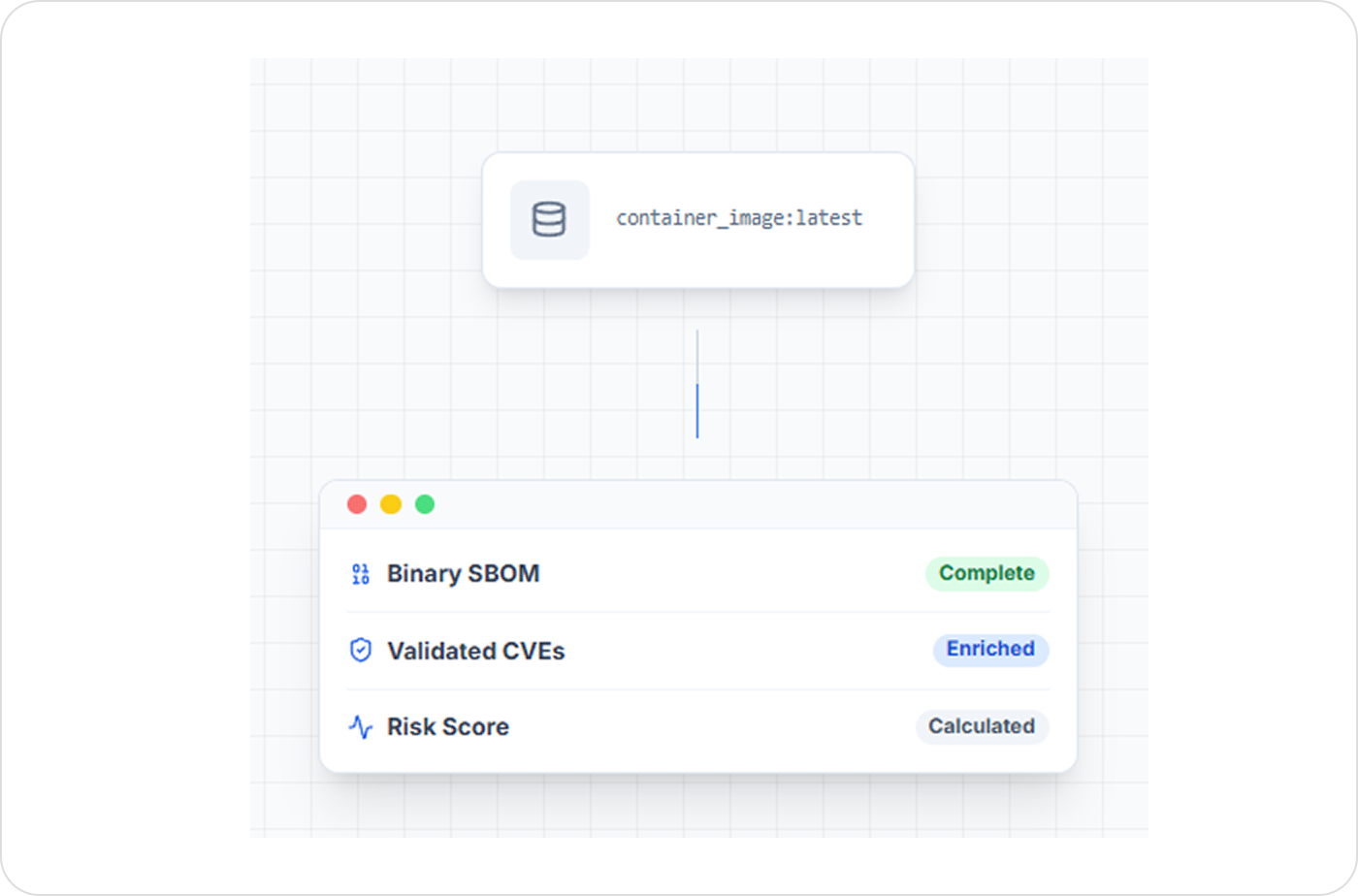
RF Profiler observes containers in real time to identify which files, libraries, and binaries are actively used. This data generates RBOM™ and isolates vulnerabilities relevant to your execution paths - reducing noise and focusing remediation where it matters.