Why AI Infrastructure Accumulates Vulnerability Risk
Dependency sprawl
Dependency sprawl across frameworks, services, and containerized components
Rapid Iteration
Rapid iteration that outpaces manual vulnerability remediation
Limited runtime
Limited runtime context to separate exploitable risk from noise
How RapidFort Reduces AI Software Risk
Prioritize True Risk with Analyzer and Profiler Intelligence


Start Secure with Curated Near-Zero CVE Foundations
Continuously Reduce Exposure with Optimizer and CART

Outcomes AI Teams Can Rely On
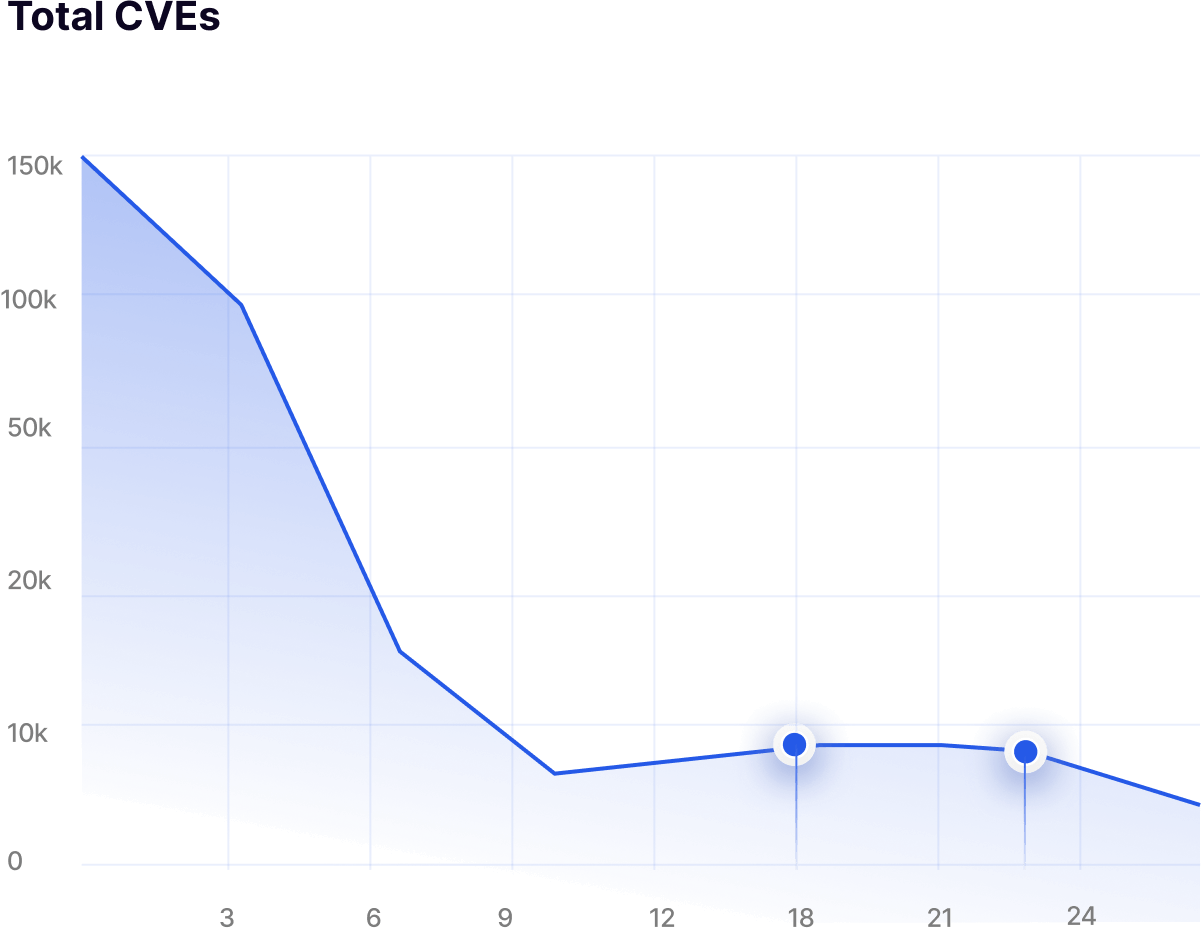
Up to 95% CVE reduction
Achieved through hardened base images and automated attack surface reduction.
Up to 90% attack surface reduction
Delivered by removing unused binaries and dormant runtime components.
Faster audit preparation
SBOM, RBOM, and configuration evidence remain continuously ready for review.
About 60% less manual remediation effort
Automation replaces repetitive vulnerability triage, exception handling, and patch cycles.
Regulatory Evidence Built Into Every Release
SOC 2 Type II
Continuous vulnerability validation and SBOM/RBOM artifacts supporting secure AI platform operations.
ISO/IEC 27001
CIS and STIG-aligned configurations with evidence mapped to Annex A controls.
FedRAMP-Aligned Cloud Environments
FIPS-validated, hardened containers with reporting that supports authorization workflows.
Platform Trust and Security Reviews
Component lineage and runtime-verified RBOM supporting customer and partner assurance.
Frequently Asked Questions
Answers to Your Most Common Questions


RapidFort is a Software Supply Chain Security platform that helps teams identify, prioritize, and remediate software vulnerabilities - without code changes - by combining DevTime Protection Tools, Curated Near‑Zero CVE Images, and RunTime Protection Tools into a Software Attack Surface Management (SASM) workflow. Typical outcomes include up to 95% CVE remediation and up to 90% attack surface reduction driven by runtime intelligence.


Step 1 — Inventory & Understand (DevTime Protection Tools):
Integrate with your CI/CD pipeline or directly into your Kubernetes environment to scan container images, generate SBOM/RBOM™, reconcile scanner findings, detect drift, and profile execution paths using binary scanning. Outputs include SPDX/CycloneDX reports and RapidRisk Score to prioritize real risk.
Step 2 - Remediate & Automate (Curated Near‑Zero CVE Images):
Drop‑in 10,000+ curated images built on LTS distributions (Alpine, Debian, Red Hat, Ubuntu), hardened with STIG/CIS in alignment with NIST SP 800‑70, with FIPS 140‑3 validation and continuous patching - so teams start with near zero CVEs. No vendor lock‑in.
Step 3 - Maintain & Defend (RunTime Protection Tools):
Enforces runtime‑guided hardening to remove unused components, continuously monitors baselines, and alerts on anomalies - achieving up to 95% CVE remediation and up to 90% attack surface reduction with <1% compute overhead.


They are production‑grade base images that are continuously patched and scanned, available across LTS Linux (Alpine, Debian, Red Hat, Ubuntu), hardened using STIG/CIS benchmarks (aligned to NIST SP 800‑70), and offered at scale (10,000+ images). They are designed to accelerate FedRAMP/CMMC/SOC 2 readiness and avoid lock‑in by using widely adopted distributions.




