The Core Challenges of Securing Modern Software
Most CVEs Are Inherited
Open-source packages and public third-party images introduce uncontrolled vulnerabilities before any code is written.
CVE Volume Outpaces Remediation
Teams drown in findings faster than they can validate or fix them.
Runtime Behavior Is Invisible
Security decisions are made without knowing what actually executes in production.
How RapidFort Secures the Software Supply Chain
Reduce inherited risk, validate runtime behavior, and maintain audit-ready evidence continuously.
Curated Images
Start from Near-Zero CVE base images built on standard LTS Linux distributions, hardened with STIG/CIS benchmarks and FIPS-validated cryptography to eliminate inherited risk

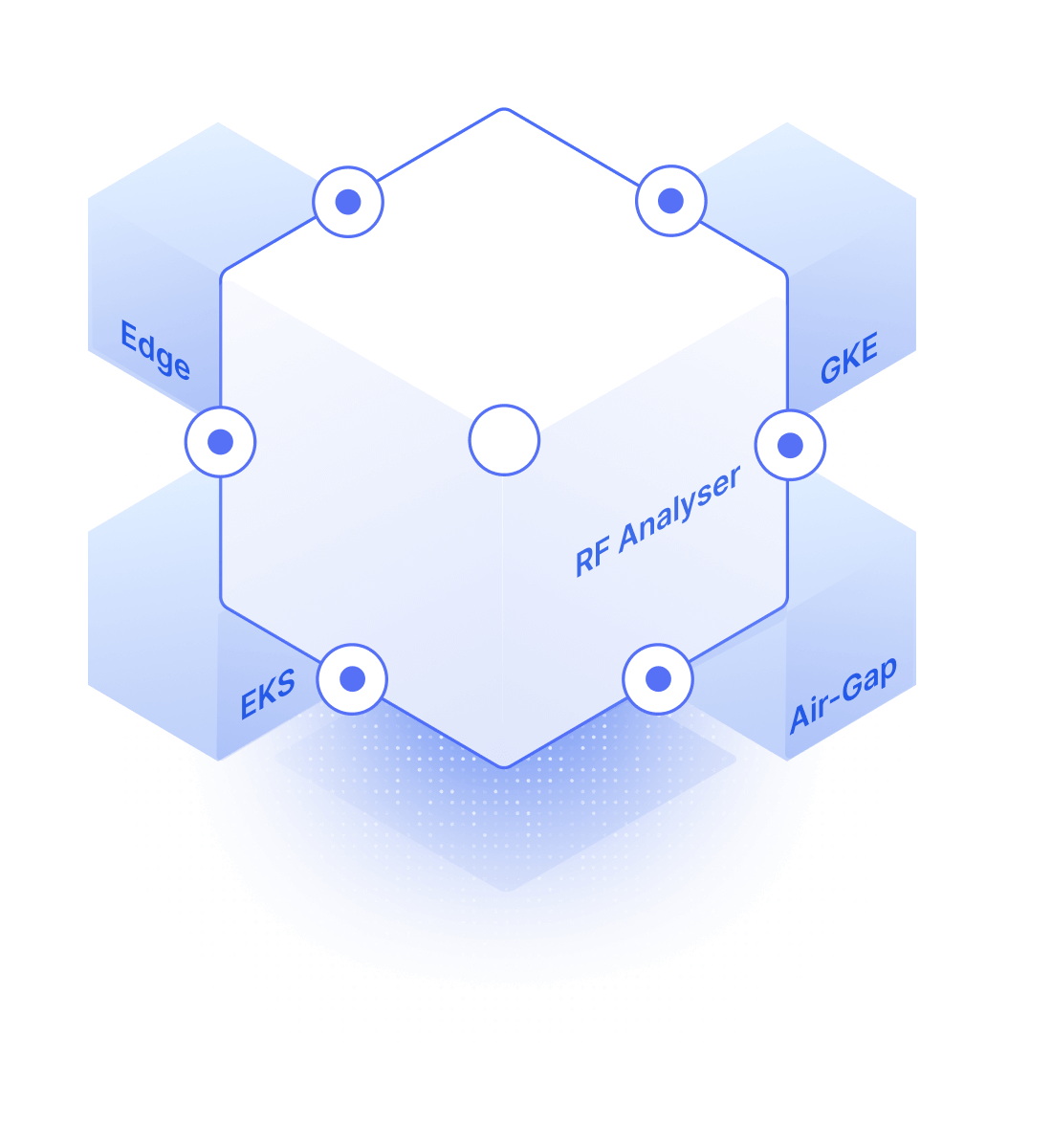
RF Analyzer
Accurately identify and prioritize applicable vulnerabilities across registries, CI pipelines, and clusters using validated, low-noise vulnerability analysis.
RF Profiler
Agentless runtime profiling that distinguishes exploitable vulnerabilities from dormant components using execution-path visibility and RBOM™.
RF Optimizer
Behavior-aware hardening that removes software bloat from containers, delivering measurable CVE and attack-surface reduction.
RF CART
Continuous compliance verification and reporting that feeds POA&Ms and self-attestation workflows without manual effort.

What Changes When Teams Deploy RapidFort
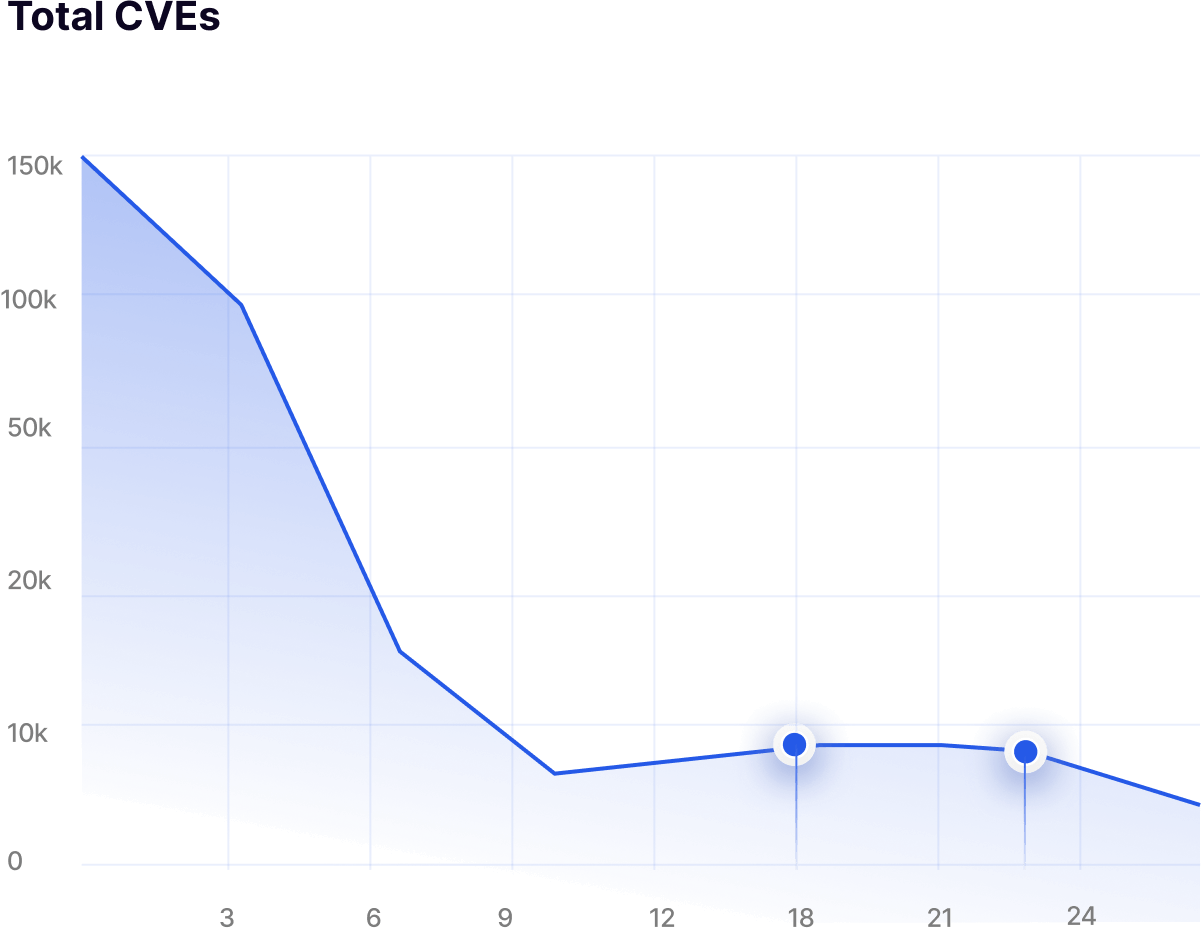
up to 95%
Total CVEs reduced by eliminating inherited and unused components
up to 90%
Total CVEs reduced by eliminating inherited and unused components
~ 60%
Reduction in manual remediation effort
Faster
Audit and authorization readiness with continuous evidence

.png)


