What Slows Authorization Readiness
CVE backlogs
CVE backlogs inherited from vendor and open-source images
Inconsistent Evidence
Continuous monitoring expectations without continuous, exportable evidence
Baseline Drift
Baseline drift across cloud, on-prem, and restricted environments
How RapidFort Reduces Mission Software Risk
Prioritize True Risk with Analyzer and Profiler Intelligence


Start Secure with Curated Near-Zero CVE Foundations
Continuously Reduce Exposure with Optimizer and CART

Outcomes Mission Programs Can Rely On
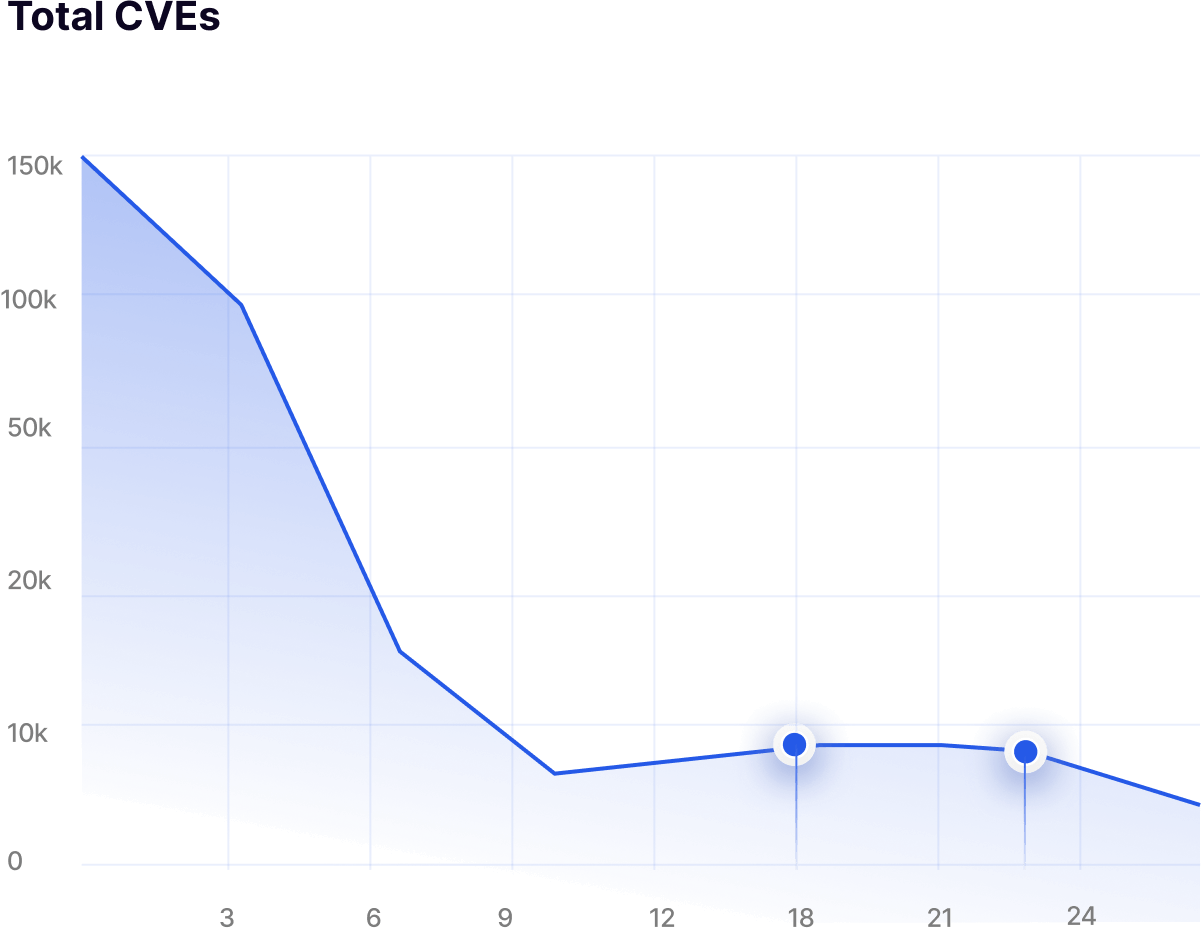
Up to 95% CVE reduction
Achieved through hardened base images and automated attack surface reduction.
Up to 90% attack surface reduction
Delivered by removing unused binaries and dormant runtime components.
Faster audit preparation
SBOM, RBOM, and configuration evidence remain continuously ready for review.
About 60% less manual remediation effort
Automation replaces repetitive vulnerability triage, exception handling, and patch cycles.
Regulatory Evidence Built Into Every Release
CMMC 2.0 and NIST 800-171
Continuous vulnerability reduction and hardened baselines supported by SBOM and RBOM artifacts.
FedRAMP and StateRAMP
STIG and CIS-aligned containers with remediation data supporting ConMon and SSP workflows.
NIST 800-53 and FISMA-Aligned Systems
Repeatable evidence mapped to federal control expectations for mission systems.
cATO and Zero-Trust Initiatives
Runtime-verified lineage, drift detection, and continuous risk reduction within authorization boundaries.
Frequently Asked Questions
Answers to Your Most Common Questions


RapidFort is a Software Supply Chain Security platform that helps teams identify, prioritize, and remediate software vulnerabilities - without code changes - by combining DevTime Protection Tools, Curated Near‑Zero CVE Images, and RunTime Protection Tools into a Software Attack Surface Management (SASM) workflow. Typical outcomes include up to 95% CVE remediation and up to 90% attack surface reduction driven by runtime intelligence.


Step 1 — Inventory & Understand (DevTime Protection Tools):
Integrate with your CI/CD pipeline or directly into your Kubernetes environment to scan container images, generate SBOM/RBOM™, reconcile scanner findings, detect drift, and profile execution paths using binary scanning. Outputs include SPDX/CycloneDX reports and RapidRisk Score to prioritize real risk.
Step 2 - Remediate & Automate (Curated Near‑Zero CVE Images):
Drop‑in 10,000+ curated images built on LTS distributions (Alpine, Debian, Red Hat, Ubuntu), hardened with STIG/CIS in alignment with NIST SP 800‑70, with FIPS 140‑3 validation and continuous patching - so teams start with near zero CVEs. No vendor lock‑in.
Step 3 - Maintain & Defend (RunTime Protection Tools):
Enforces runtime‑guided hardening to remove unused components, continuously monitors baselines, and alerts on anomalies - achieving up to 95% CVE remediation and up to 90% attack surface reduction with <1% compute overhead.


They are production‑grade base images that are continuously patched and scanned, available across LTS Linux (Alpine, Debian, Red Hat, Ubuntu), hardened using STIG/CIS benchmarks (aligned to NIST SP 800‑70), and offered at scale (10,000+ images). They are designed to accelerate FedRAMP/CMMC/SOC 2 readiness and avoid lock‑in by using widely adopted distributions.




