Unused libraries, binaries, and frameworks often contain vulnerabilities even when never executed by the application.
Security patches fix individual CVEs but leave unused OS layers and dependencies embedded inside container images.
Without runtime intelligence, teams cannot safely determine which components can be removed without breaking applications.
Uses RBOM runtime intelligence to identify components that never execute and safely remove them while preserving application functionality.


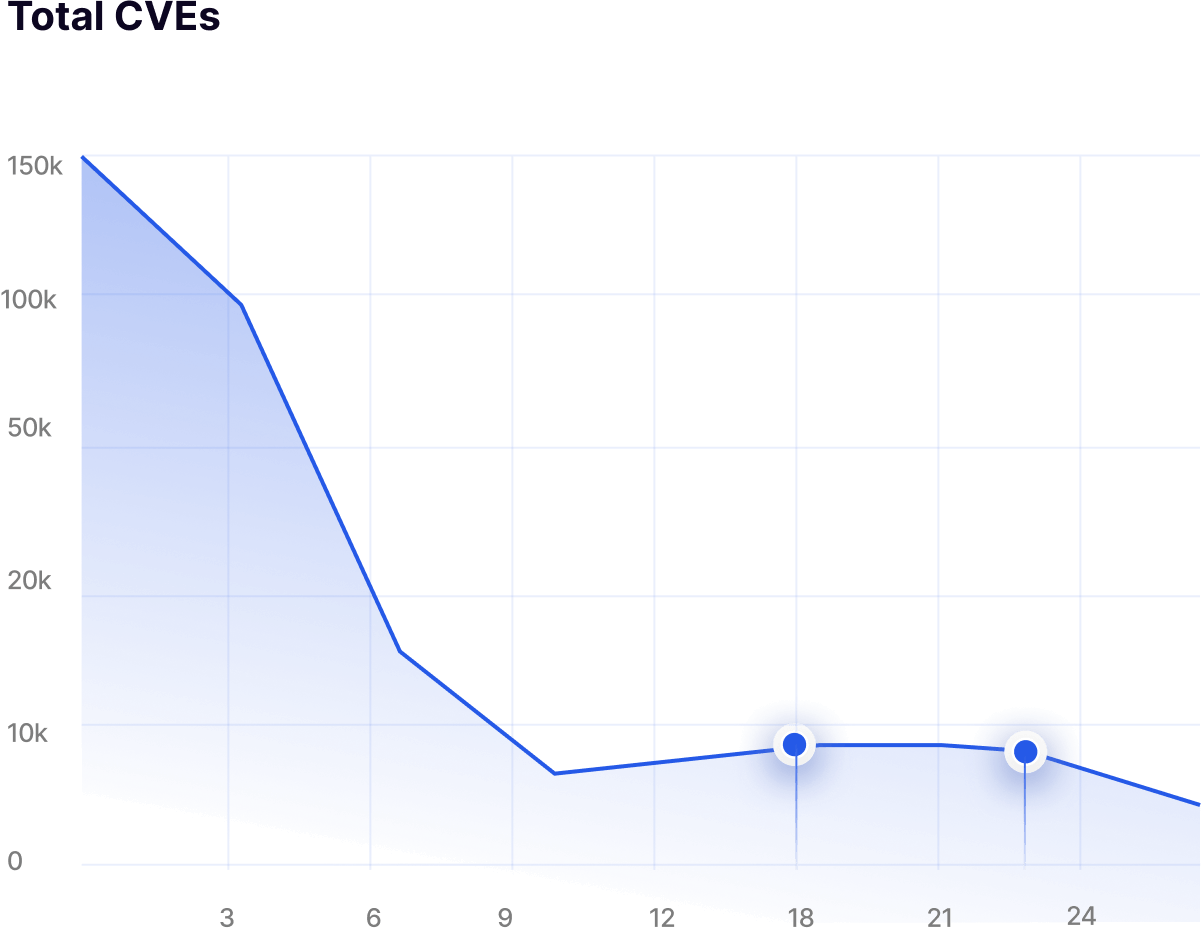
Eliminates vulnerable code paths and unused dependencies, lowering exploitable CVE exposure by up to 99.9%.
Optimization decisions are validated against real runtime execution paths. Optimized images are rebuilt every 24 hours and delivered as drop-in replacements without CI/CD changes.


Choose Light, Standard, or Aggressive hardening levels to control how aggressively unused files, packages, and dependencies are removed.
Remove vulnerable components that never execute in production.
Eliminate unused binaries, libraries, and dormant runtime components.
Hardening occurs at the container image layer without modifying code.
Smaller images improve startup time and operational efficiency.