Reduce inherited risk, validate runtime behavior, and maintain audit-ready evidence continuously.
A continuously updated record of components actually executed during runtime across container workloads.
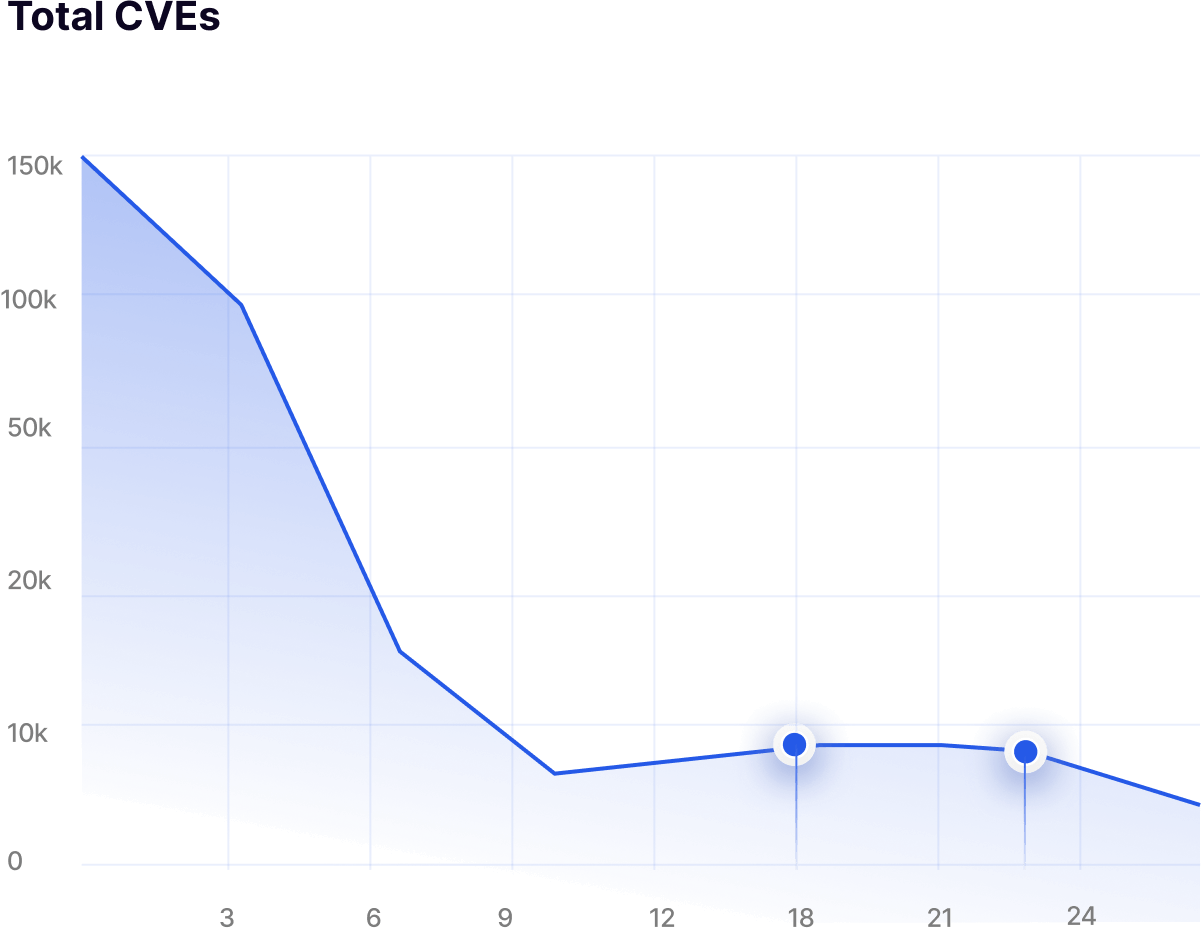
Distinguishes active code paths from dormant layers to significantly reduce vulnerability triage noise.
Establishes expected runtime behavior and flags unexpected binaries, configurations, or execution patterns.
Lightweight runtime profiling designed for Kubernetes environments with less than 1% operational overhead.
Identify CVEs tied to executed binaries and services so teams focus on vulnerabilities that represent real exposure.


Detect unauthorized binaries, configuration changes, or unexpected runtime behavior across container environments.
Use runtime execution data to safely remove unused packages, libraries, and components without breaking applications.

Achieved by identifying and removing unused components that contain vulnerabilities but are never executed.
Driven by safely eliminating dormant binaries, packages, and libraries across container images.
RBOM visibility shows exactly which components are active in production environments.
Continuous runtime profiling with less than 1% overhead and no application changes required.